BLUF
Countering Intel/Surveillance can be loosely categorized into 4 categories; Detection (surveillance and investigations) and Deterrence (security systems and procedures) – both defensive actions – as well as Deception (disinformation) and Neutralization (taking people or resources off the board) – both offensive actions.
Detection
Detection of the surveillance or intel gathering activities can be done by investigation, security procedures, notification by a third party, or by luck (though we don’t recommend relying on this one).
Running Surveillance Detection Routes (SDR) when you are mobile can help to spot a “tail” (someone who is following you). Random perimeter/property sweeps of your house or property can help to spot electronic surveillance (bugs) or a nearby eavesdropping team. Both are easy to implement.
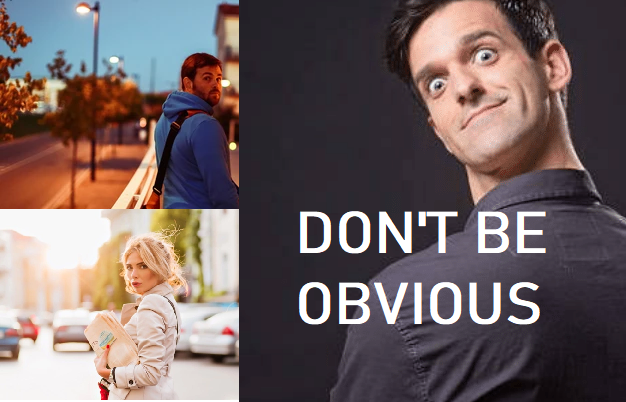
Depending on the situation, private investigators, law enforcement, or a security consultant may be necessary. An obvious on the street example is maintaining awareness of your surroundings with a discreet glance over the shoulder. A NON-OBVIOUS glance. You can also apply detection techniques to your house or neighborhood.
Deterrence
Deterrence is an overt show of force. Your security procedures and precautions may need to be observable in order to deter anyone. Being gray, not being outwardly cautions, may make it appear as if you’re not aware or you don’t have protection. Sometimes it’s best to become a hard target by flexing your “muscle.”
Let others know you’re watching, “burn” them. Let them know the police have been called, that you carry a weapon, or that you know they’re watching you. THIS COULD ACTUALLY MEAN BEING OBVIOUS WITH A COMPLETE STOP ON THE SIDEWALK FOLLOWED BY A STARE AT THEM, MAKING THEM AWARE YOU KNOW THEY’RE FOLLOWING.
Consider security cameras, proper landscaping, high walls, fences, dead bolt locks, barred windows, guard dogs, controlled access points, or if you’re on a budget, even a sign that says you have any of these things can be a deterrent.
If you want to see more detail on deterrence and detection techniques, see our previous article.
Deception
Deception or disinformation is an offensive form of counter-intelligence. In simple terms; lying, distractions, and false fronts.
On the personal level, for most, the biggest threat here is data aggregators and brokers. Others may research or “skip trace” using these online resources. Use it against them by entering false or misleading information when you create website accounts, or fill out surveys. Sign-up for various services or websites and enter semi-factual info, enough so that it can be scraped by Spokeo or MyLife (people search databases). You can also create accounts and edit your profiles on many of the aggregate pages in order to edit data they’ve already discovered.
Also make it seem like there is someone home when you’re not (lights on and TV going). Make it appear there are more people living on your property than there really are (additional cars, clothes on a clothesline).
Neutralization
Neutralization is an offensive action and it can mean lethal force IF NECESSARY. This is rarely the case. Unless your life or someone else’s is in danger and non-lethal force is not an option, avoid it.
Neutralization can also mean removing an enemy’s pieces from the board: taking them out of play in some manner (blackmail, restraining order, threats) or making it so that they are no longer effective. This can be done in a wide range of ways based on the situation, ranging from covert to completely overt. However in most situations, to remain legal, this will be done by involving some kind of law enforcement.
Debrief
Which of the 4 categories you use will depend on your situation and should be based on your evaluation of the threat. However, a layered approach of deception, detection, and deterrence will be most successful in prevention. You should save neutralization only for when the other approaches fail.
If you become aware of a threat to your life or your family; you should involve law enforcement (LE) as soon as possible (as long as rule of law remains). Even if they can’t immediately do anything, due to no crime being committed, they may be able to offer some protection (deterrence) or investigative (detection) help. If criteria is met, they could pursue charges of stalking, harassment, etc. If LE can’t aid; follow the 4 steps.
The real question is why are you being watched? Answer that first! Then resolve the root cause.
This article was originally written by the Grayman Briefing. Stay in the know, sign up for Intel and Situational Awareness alerts pushed to your phone on emerging threats and preparedness warnings. Click HERE to subscribe to the Grayman Briefing.
=====
Become a Survival Dispatch Insider …
We bring together survival enthusiasts and preppers to share skills and knowledge, so you can enhance your preparedness for emergencies and ensure the safety of you and your community.
The Results You’ll Get …
Our community, courses, and memberships are pretty special. We focus on the ways it will make a huge difference in your life.
Here are a few of the things you’ll be able to do as a member of Survival Dispatch Insider …
1) Improve your emergency preparedness by learning survival skills and strategies from experienced preppers.
2) Build lasting connections with like-minded individuals that share your passion for safety and readiness.
3) Access a wealth of knowledge and resources to assist in protecting you and your community during unexpected situations.
Click HERE to get started.
=====