The idea of secret off-grid communication is not limited to survivalists. The word that describes this idea is “cryptography” which is the study or practice of secure communication. The practice goes back at least thousands of years. Like most aspects of tradecraft, success is predicated on hard common sense and attention to detail. Especially related to all things security. Attention to detail in security matters is an essential habit of effective survivalists. My experience reinforces that of former CIA Director Allen Dulles’ writing on intelligence work. The entire article this quote came from is worthy of study but the following excerpt illustrates my point:
“3. In any case, the man or woman who does not indulge in the daily security routine, boring and useless though it may sometimes appear, will be found lacking in the proper instinctive reaction when dealing with the bigger stuff.
4. No matter how brilliantly given an individual, no matter how great his good will, if he is lacking in security, he will eventually prove more of a liability than asset.”
A damning and sobering appraisal of many a survivalist, and even many operators. No matter how many times you’ve played on the two-way shooting range, how frosty you are, or how smart you are, you can’t neglect security. Neglecting security details makes you nothing more than a liability.
Security for Private Communication
Given who I am, who you are, and why you’re interested in this topic, I’m not going to try to cover my backside with a sanctimonious lament about how this information could be misused. I don’t think it’s the least bit shady to explain to regular folks how to keep their private matters private. No, the shady part is that the scales are heavily weighted against anyone who wishes any degree of privacy.

My wish is that more survivalists would apply what I teach about privacy. However, most have an addiction that prevents them from doing so. They’re addicted to convenience and it compels them to trade their right to privacy for whatever small measure of convenience the tech sector happens to be peddling this quarter.
On a technical note, by untraceable I actually mean not traceable back to you! Other than that, I’m going to keep most of this article as non-technical as possible. I want to keep it as useful as possible to the majority.
Compartmenting
The biggest way that people bungle untraceable communications is failing to properly compartment. There are plenty of ways to leave a trail to follow. However, a disproportionate number of mistakes that get people discovered sending secret communications are due to poor compartmenting.
Most people have an identity by which they are known to the government, which I’ll call the legal name. Legal names get used to pay taxes, are typically associated with a social security number, one or more phone numbers, addresses, a credit score, fingerprints, email addresses, credit card numbers, internet access, probably social media accounts, and so on.
Undercover operatives, spies, criminals, authors, celebrities, hackers, victims, and others use alternate identities to protect themselves, their families, and compatriots. Good guys call these names alternate identities, callsigns, pen names, or stage names when they’re used by good guys. Aliases or street names when they’re used by bad guys. Clever operatives have “shelf IDs” that are setup in advance and parked just waiting for a purpose. Creating them in advance and maintaining it isn’t convenient. Social media did away with entire rings of spies, snapped up because their alternate identities were city-dwellers young enough that they should have had social media accounts. Lack of information can be every inch the red flag that information can.
Compartmented identities help keep people safe as long as their enemies aren’t able to associate their alternate identity with their legal name. People used to use alternate names all the time.
Burner Phones
It has been written that an extraterritorial visitor to our planet could be forgiven for mistaking cell phones for life-sustaining technology or even some type of appendage of the human body. As long as the cell system is up, cell phone communications will certainly be the go-to medium of communication for most people. Smartphones are useful for much more than just their communications capability.

At the time of this writing, obtaining and operating a burner phone in the US isn’t that difficult. There are ways to screw it up though, especially if you’re convenience addicted. The main way to bungle traceless communications is poor compartmenting. Compartmenting is about 10% understanding technology and 90% common sense. Did I mention that burner phones should be small? Because you’re going to need more than one to do much good.
Compartmenting Applied to Burner Phones

Identities
No aspect of the identity associated with your legal name can have anything to do with any of your burner phones at any point. One way to screw that up is to have burner phones in your possession, vehicle, or home when everything in them is entered into evidence. For this reason, burner phones should be stored in off-site caches, not in your bug out bag. I have seen this on more than one so-called tactical site. Caches should be pit stops near hole up sites, safe houses, or near routes of exfil.
Electronic Devices
Electronic devices for network communication have unique numbers that identify them. The devices used by your legal name shouldn’t ever be used by your other identities.
Location
The position of a cell phone can be triangulated by cell towers even if the GPS is turned off. This means that the path of your smartphone, while it has a battery in and it’s outside the shielded pouch must not intersect the path of your cell phone at any point.
Time Stamps
If your smartphone is normally very active but is turned off/inactive the same times that the burner phones used by an alternate identity are active, that could also get you found.
Street Address and Phone Number
Depending on the phone, you’ll need to call it from another cell phone or landline to activate it and may have to give a street address. Any address not associated with your legal name should do. In cases where it doesn’t, research the term “ghost address” which has been written about in detail by privacy consultant J.J. Luna. For phone numbers, that’s what hotels are for. They’re great for activating bank cards too but not both at the same hotel or at the same time. Seeing a pattern of common sense here? You should be.
Accounts
Burner phones are best bought with cash at swap meets and street fairs. Don’t use bank cards or credit cards that share names or addresses with the identity associated with your legal name.
Facial Recognition
Don’t buy burner phones from places with cameras. Discreetly recon with a lens finder if you have any doubt. Change/obscure your appearance when buying burner phones so you don’t get identified by a human being.
Transportation
For many years, police cruisers and tow trucks have been outfitted with Automatic License Plate Recognition (ALPR) technology. Every plate they scan is fed into a nationwide database that records were your vehicle was and when it was there with precise GPS data. That information may be kept indefinitely. Now anyone can get in on the act by downloading free open source ALPR software. By only installing plates on the rear of your vehicles where it’s legal. Then by backing into parking spaces, you can greatly reduce your exposure to this technology. This is also a reason to arrive at the places you buy burner phones via untraceable transport.
Burner Phones Should Have a Short Lifespan
As the name implies, burner phones are to be used for a single call or job and then the phone is “burned”. This means it’s now too risky to use. As minutes turn to hours, risk goes up exponentially. Ideally, you’ll use the phone once then pull the battery, sanitize the phone, and make it disappear. Most service plans are thirty days but can be up to ninety. If it could be a while before the phone is used, Tracfone minutes can be good for up to a year depending on the plan.
Cell Service Providers
You’ll notice that I talk about my “burner phones” in the plural as opposed to my “burner phone” in the singular. A single burner phone is a one-shot deal. Buy phones from different providers, different states, or better yet, from different countries.
Fingerprints
Wear gloves and carry a handkerchief.
TAILS
TAILS stand for The Amnesic Incognito Live System. It’s a live operating system that runs from a USB or DVD. The system can be used on most computers to gain access to the TOR network and includes tools which enable the encryption of files, emails, and instant messaging … all without leaving any trace on the computer you force to do your bidding. These days, a survivalist should have at least a couple of tiny USB sticks on his or her person. The most current version of TAILS should be on at least one of them.
Orbot & Orfox
Orbot enables anonymous email, internet access, and instant messaging over Android phones courtesy of the good folks at TOR. Orfox is a TOR web browser for Android built to maintain anonymity. Used together, they enable mobile phone users to access the web, send instant messages, and emails without being monitored or blocked by the mobile internet service provider. So, burner phone + Orbot + Orfox (run from a USB stick with USB and MicroUSB OTG connectors) = anonymous web browsing, email, and instant messaging.
Vuvuzela
You have probably heard of, and may use, TOR which has been a useful tool for over a decade. It is pretty good and has protected millions of users. There have also been a few cases where it’s fallen short. The trouble with TOR is when it was designed, the designers couldn’t have imagined living in a world where every single node was monitored. They also couldn’t have imagined an adversary powerful enough to control large numbers of nodes on the TOR network. That they would make TOR vulnerable to traffic analysis. That was before Snowden made the world aware of the extent of overreach and abuse of power that had occurred.
Enter Vuvuzela. What Vuvuzela does is it protects both the content of the message and the metadata that could reveal the sender of that message and mixes it with enough noise to thwart traffic monitoring. Using Vuvuzela with Alpenhorn, all that’s needed is your friend’s username, usually an email. You can start chatting on Vuvuzela without having to exchange encryption keys in person. It’s IT Security, the process of exchanging encryption keys over an empirical channel is known as bootstrapping.
One-way Pagers
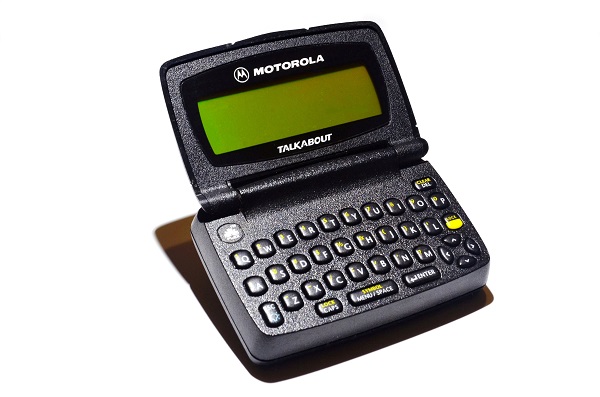
As long as you or your technology only receives radio signals and doesn’t transmit, there’s no way to be located. Cell phones can be located because they’re constantly being pinged by cell towers. Friendlies with the ability to contact you can use a pre-arranged communications plan to pass information.
Since one-way numeric pagers don’t require the user to listen for messages at a certain time, they’re particularly effective in this role. The signals that pagers receive are far more powerful than those of cell phones. Pagers continue to receive pages in the depths of large buildings like hospitals, where cell phone calls tend to drop. Since pagers only receive and don’t send, they’re far less power hungry than cell phones and last a very long time on a charge or battery. Pager networks also have a degree of redundancy that cell networks lack.
GSMK Cryptophone

Got a few thousand plus burning a hole in your pocket? GSMK Cryptophones out of Germany offers opensource encryption code. Just secure your communications or have an IT professional you trust verify it.
Final Thoughts
In summation, old school or low-tech tactics are effective even against high technology. The threats you face determine what tradecraft is most applicable to you and your pattern of life. Compartmenting is about 10% understanding technology and 90% common sense. In security work, the little things are the big things. Neglect security details and you’re a liability to any organization … end of story.
Sensitive information on paper is dangerous. Encrypted and off-line, like on a flash memory not plugged into an internet connected computer, is generally safer. Sensitive material put on paper should be in a code that only you understand. TAILS (The Amnesic Incognito Live System) is a live operating system that can be run on most computers from a USB Stick that leaves no trace. Orbot is TOR functionality for Android and Orfox is TOR’s browser for Android phones. Vuvuzela is a text messaging system designed to protect against even the most powerful adversaries capable of traffic analysis. It just takes a few extra steps to make yourself secure and not a liability.
This article was originally published in Survival Dispatch Insider magazine Volume 2 Issue 2.
=====
Become a Survival Dispatch Insider …
We bring together survival enthusiasts and preppers to share skills and knowledge, so you can enhance your preparedness for emergencies and ensure the safety of you and your community.
The Results You’ll Get …
Our community, courses, and memberships are pretty special. We focus on the ways it will make a huge difference in your life.
Here are a few of the things you’ll be able to do as a member of Survival Dispatch Insider …
1) Improve your emergency preparedness by learning survival skills and strategies from experienced preppers. 2) Build lasting connections with like-minded individuals that share your passion for safety and readiness. 3) Access a wealth of knowledge and resources to assist in protecting you and your community during unexpected situations. Click HERE to get started.
=====